API Security with OAuth 2.1: A Practical Implementation Guide
A practical blueprint for implementing OAuth 2.1 for APIs: PKCE, sender-constrained tokens, secure flows for web, SPA, mobile, and machine-to-machine.
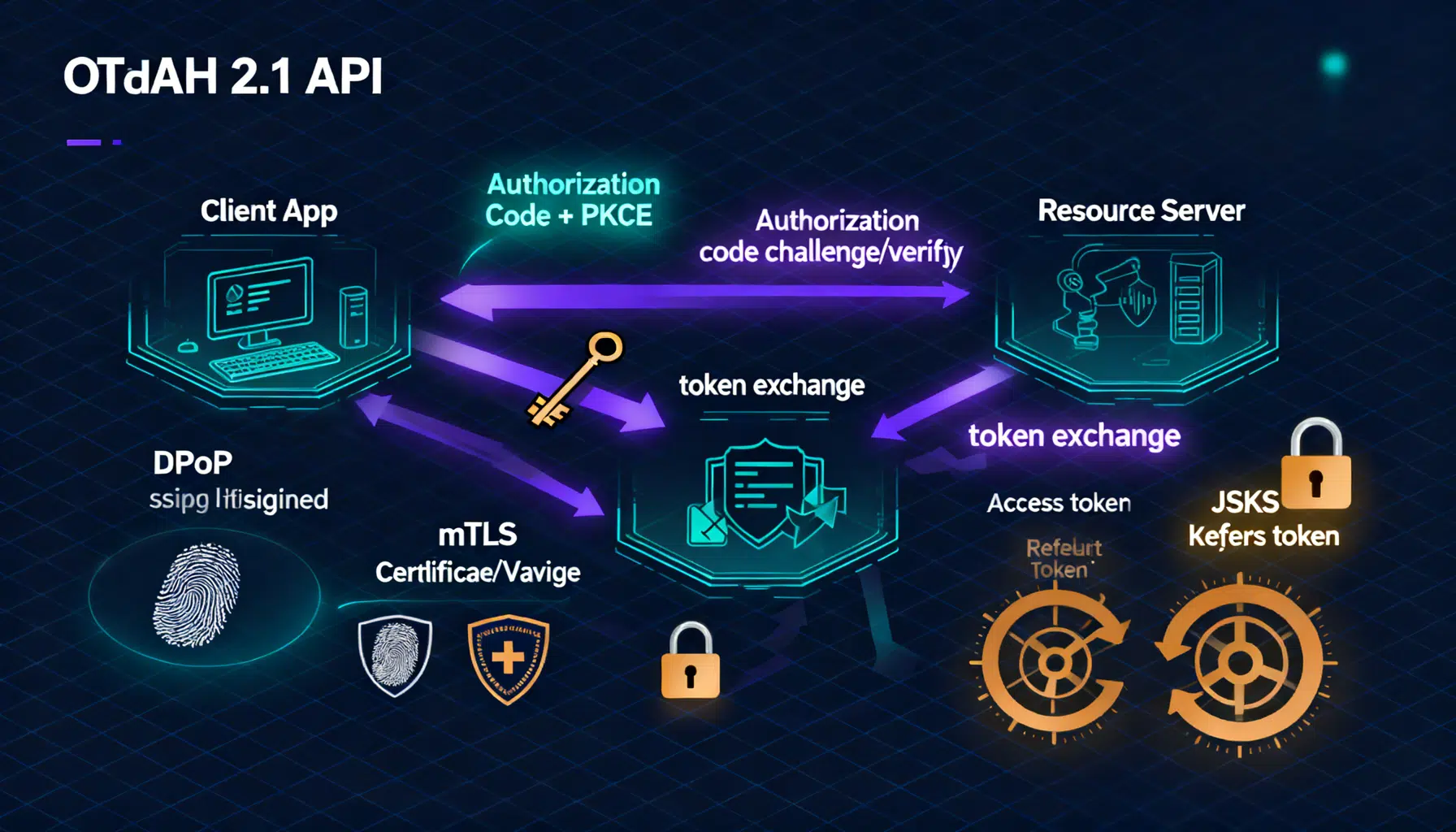
Image used for representation purposes only.
Overview
OAuth 2.1 is a consolidation of the OAuth 2.0 framework and its widely adopted security best practices. It removes risky grants, mandates stronger defaults like PKCE, and tightens redirect handling and token hygiene. The result: fewer foot‑guns for implementers and a more robust baseline for securing APIs.
This guide walks you through implementing OAuth 2.1 for real-world APIs—covering architecture, flows, code samples, sender‑constrained tokens (mTLS/DPoP), SPA and mobile nuances, and an operational checklist you can ship with.
Core roles and building blocks
- Authorization Server (AS): Authenticates users/clients, issues tokens.
- Resource Server (RS, your API): Validates tokens, enforces scopes/claims.
- Client: The app calling the API (confidential server app, public SPA/native app, or machine client).
- Tokens:
- Access token: Short‑lived credential presented to the API.
- Refresh token: Long‑lived credential used by the client to obtain new access tokens. Rotate or sender‑constrain it.
- Scopes and claims: The least‑privilege contract between client and API.
What OAuth 2.1 changes (and why it matters)
- Authorization Code with PKCE for all public clients; PKCE recommended for confidential clients too.
- Implicit and Resource Owner Password grants are removed.
- Exact redirect URI matching is required; dynamic wildcards are out.
- Refresh token rotation and revocation are recommended; sender‑constrain where possible.
- TLS is mandatory; no plaintext redirects or token transport.
- Stronger defaults for state/nonce, and protection against code injection/replay.
Reference architecture
- Client (browser, mobile, server) initiates Authorization Code + PKCE via the Authorization Server.
- AS issues short‑lived access tokens (JWT or opaque) and optional refresh tokens.
- API validates each request’s token: locally (JWT) or via introspection (opaque).
- Optionally constrain tokens to the client using mTLS or DPoP to reduce replay risk.
- Centralized key management (JWKS) with rotation; metrics and audit logs across AS and APIs.
End‑to‑end: Authorization Code + PKCE
Below is a minimal, hardened baseline that works for web apps, SPAs, and mobile.
- Create a PKCE verifier/challenge
- Verifier: high‑entropy random string (43–128 chars)
- Challenge: base64url(SHA‑256(verifier)) using the S256 method
Example (JavaScript):
// PKCE S256 generation
async function pkce() {
const bytes = new Uint8Array(32);
crypto.getRandomValues(bytes);
const verifier = btoa(String.fromCharCode(...bytes))
.replace(/\+/g, '-').replace(/\//g, '_').replace(/=+$/, '');
const digest = await crypto.subtle.digest('SHA-256', new TextEncoder().encode(verifier));
const challenge = btoa(String.fromCharCode(...new Uint8Array(digest)))
.replace(/\+/g, '-').replace(/\//g, '_').replace(/=+$/, '');
return { verifier, challenge, method: 'S256' };
}
- Start the authorization request
- Include response_type=code, code_challenge, code_challenge_method=S256, state (CSRF protection), and exact redirect_uri.
GET /authorize?
response_type=code&
client_id=your_client_id&
redirect_uri=https%3A%2F%2Fapp.example.com%2Fcallback&
scope=api.read%20api.write&
state=Zy9x...&
code_challenge=E4i...&
code_challenge_method=S256 HTTP/1.1
Host: auth.example.com
-
User authenticates and consents at the AS.
-
AS redirects back with an authorization code and the original state.
HTTP/1.1 302 Found
Location: https://app.example.com/callback?code=SplxlOBeZQQYbYS6WxSbIA&state=Zy9x...
- Exchange code for tokens (use the code_verifier). For confidential clients, authenticate with client_secret or private_key_jwt.
POST /token HTTP/1.1
Host: auth.example.com
Content-Type: application/x-www-form-urlencoded
grant_type=authorization_code&
code=SplxlOBeZQQYbYS6WxSbIA&
redirect_uri=https%3A%2F%2Fapp.example.com%2Fcallback&
client_id=your_client_id&
code_verifier=v3r1f13r...
AS response:
{
"access_token": "eyJhbGciOi...",
"token_type": "Bearer",
"expires_in": 900,
"refresh_token": "def50200...",
"scope": "api.read api.write"
}
- Call the API with the access token
GET /v1/profile HTTP/1.1
Host: api.example.com
Authorization: Bearer eyJhbGciOi...
- API validates the token
- JWT: Verify signature, issuer, audience, expiry, and scope. Cache JWKS keys, honor kid and key rotation.
- Opaque: Introspect with the AS over mTLS; cache positive results briefly, negative results minimally.
- Renew tokens safely
- Use refresh token rotation (every use returns a new refresh and invalidates the old one).
- Sender‑constrain refresh tokens with mTLS or DPoP where feasible.
- Immediately revoke on suspicion of compromise.
Sender‑constrained tokens: mTLS vs DPoP
Bearer tokens are transferable. Constraining them to the client reduces replay risk.
-
mTLS (Mutual TLS)
- Access/refresh tokens bound to the client’s X.509 certificate.
- Strong protection for server‑side and enterprise clients.
- Operational overhead: certificate provisioning and rotation.
-
DPoP (Demonstration of Proof‑of‑Possession)
- Works at the HTTP layer using an ephemeral key pair.
- Client signs a DPoP proof (header) per request; the AS binds tokens to the DPoP public key.
- Ideal for SPAs and mobile where certificates are harder.
Choose based on client type, device control, and infrastructure maturity. Both approaches materially curb token replay.
Designing a resource server that’s hard to break
- Accept tokens only over HTTPS. Reject tokens in query parameters.
- Validate:
- Signature (JWT) or introspection result (opaque)
- iss/aud alignment with your API
- exp/nbf with small clock skew (<= 60s)
- scope/claims mapped to your authorization policy
- Enforce least privilege: narrow scopes per endpoint; prefer fine‑grained, API‑native authorization checks.
- Return precise errors:
- 401 with WWW-Authenticate for invalid/expired tokens
- 403 for insufficient scope
Example error response:
HTTP/1.1 401 Unauthorized
WWW-Authenticate: Bearer error="invalid_token", error_description="expired access token"
SPA, mobile, and server‑side patterns
-
SPAs
- Use Authorization Code + PKCE.
- Keep tokens in memory, not localStorage; consider a Backend‑for‑Frontend (BFF) to hold tokens in httpOnly, SameSite=strict cookies.
- Avoid embedded webviews for login; use the system browser.
-
Mobile (native)
- Authorization Code + PKCE with claimed HTTPS redirect URIs (iOS Universal Links / Android App Links).
- Avoid custom schemes unless you implement strict app‑link verification.
-
Server‑rendered web apps
- Confidential client with private_key_jwt or client_secret; store refresh tokens securely server‑side.
- Consider mTLS for high‑trust environments.
-
Machine‑to‑machine
- Use client credentials grant with narrow scopes and short‑lived tokens.
- Prefer private_key_jwt and mTLS; rotate keys regularly.
Hardening the authorization server
- Enforce exact redirect URI matching; pre‑register known redirects.
- Mandate PKCE S256; reject plain and missing challenges for public clients.
- Use state and (where appropriate) nonce; bind state to user session.
- Rotate refresh tokens; detect replay and revoke the family.
- Support JWKS and automated key rotation with short kid lifetimes.
- Offer PAR (Pushed Authorization Requests) to keep request parameters off the front channel.
- Support mTLS and/or DPoP for sender‑constrained tokens.
- Emit detailed audit events for consent, token issuance, revocation, and key changes.
Operational concerns you shouldn’t skip
- Secrets and keys
- Store client secrets and private keys in an HSM or cloud KMS.
- Automate rotation; monitor for stale or overlapping keys.
- Logging
- Never log full tokens; log only hashes/fingerprints and kid.
- Redact authorization codes and PII in traces.
- Rate limits and abuse protection
- Throttle /authorize, /token, /introspect, and /revocation endpoints.
- Apply bot detection to high‑risk tenants/clients.
- Timeouts and retries
- Use idempotency keys for token exchange retries; back off aggressively.
- Backups and DR
- Snapshot client registrations and JWKS; test restore and failover.
Migration path from OAuth 2.0 to 2.1
- Inventory all clients and flows; find implicit/password grants and SPAs using tokens in URLs or storage.
- Move to Authorization Code + PKCE everywhere; drop implicit/password grants.
- Enforce exact redirect matching; remove wildcards.
- Shorten access token lifetime; enable refresh token rotation.
- Introduce sender‑constrained tokens (DPoP for SPAs/mobile, mTLS for server/m2m) where feasible.
- Adopt PAR for sensitive clients to reduce front‑channel leakage.
- Harden logging, revocation, and key rotation; publish JWKS and automate rollover.
Minimal code and config checklist
-
Client
- Generates high‑entropy PKCE verifier; uses S256 challenge
- Stores state and validates on callback
- Exchanges code with code_verifier over TLS only
- Uses refresh rotation; handles reuse detection gracefully
- Implements DPoP (public clients) or mTLS (confidential/m2m) when available
-
Authorization Server
- Exact redirect URI matching
- PKCE required for public clients; S256 only
- Refresh token rotation and family revocation
- JWKS with automated key rotation
- Optional PAR; rate limits on /token and /introspect
-
Resource Server (API)
- Validates signature/issuer/audience/expiry/scope
- Enforces least‑privilege scopes per endpoint
- Returns proper 401/403 with WWW‑Authenticate details
- Supports DPoP/mTLS verification when tokens are bound
Final thoughts
OAuth 2.1 isn’t a new paradigm; it’s the safer subset and the practical default. By adopting Authorization Code + PKCE, exact redirects, short‑lived tokens, refresh rotation, and sender‑constrained tokens, you dramatically shrink your attack surface. Pair these with disciplined key management, precise API authorization, and strong operational hygiene, and your APIs will stand up to modern threats with confidence.
