FBI didn’t crack Signal—iOS notification previews let agents read “deleted” messages on a seized iPhone
FBI recovered incoming Signal messages from an iPhone’s notification storage—without breaking encryption. Here’s what happened and how to lock down previews.

Image used for representation purposes only.
FBI recovered “deleted” Signal messages from an iPhone — by reading iOS notification storage
A freshly revealed courtroom detail shows the FBI pulled copies of incoming Signal messages from a defendant’s iPhone even after the app had been deleted. The content wasn’t taken from Signal’s servers or by breaking Signal’s end‑to‑end encryption. Instead, investigators extracted text that iOS had saved locally as notification previews, according to reporting from 404 Media and corroborating tech outlets on April 9–10, 2026. (404media.co )
What happened
During a Texas prosecution tied to vandalism and a July attack on the Prairieland ICE Detention Facility, FBI testimony described how agents recovered incoming Signal messages from the iPhone’s internal notification database. A summary shown in court reportedly stated: “Messages were recovered … through Apple’s internal notification storage—Signal had been removed, but incoming notifications were preserved in internal memory. Only incoming messages were captured (no outgoing).” (heise.de )
Multiple outlets picked up the account, emphasizing that the recovery stemmed from iOS’s handling of lock‑screen and banner notifications when previews are enabled. Those previews can persist in system databases even if the user later deletes the app. (404media.co )
What was—and wasn’t—cracked
- Not Signal’s encryption: Signal retains virtually no user data on its servers beyond basic account timestamps, and it cannot hand over message content even under subpoena. The case at issue involved data resident on the device, not data obtained from Signal. (signal.org )
- Yes, Apple’s local notification store: iOS saved text that appeared in notification previews for incoming messages; that database was later extracted during a forensic exam. (heise.de )
This distinction mirrors the broader reality of device forensics: once investigators have a phone in hand and can perform a file‑system extraction, they can often recover app data and system artifacts—even when messages inside a secure app remain end‑to‑end encrypted in transit. (enterprise.cellebrite.com )
How investigators likely did it
Modern mobile forensics platforms can perform “full file system” (FFS) or partial extractions on supported, lawfully accessed iPhones. Those extractions target system databases and third‑party app sandboxes to recover deleted or residual records, including notification stores, journaling files, and other artifacts. That’s why incoming message text that once flashed on the lock screen can later reappear in an examiner’s report. (enterprise.cellebrite.com )
The approach is not new in principle. In earlier high‑profile cases, investigators recovered encrypted‑app chats from seized devices after improved extraction passes captured app databases and artifacts that weren’t obtained the first time. (arstechnica.com )
Why “deleted” didn’t mean gone
On iPhones, users can choose to show notification previews “Always,” “When Unlocked,” or “Never.” If previews are allowed, iOS can store the preview text in its notification database so it appears in the Notification Center and on the lock screen—content that may persist even if the app is later removed. That’s the cache the FBI described accessing in this case. (support.apple.com )
Notably, this method recovers only what iOS displayed as incoming notifications on that device. Outgoing messages (which wouldn’t have been previewed in notifications) were not recovered, underscoring that the technique leverages iOS behavior rather than an encryption break. (heise.de )
What this means for users of secure messengers
- End‑to‑end encryption still protects messages in transit and on providers’ servers when designed like Signal’s, but device‑level artifacts can leak content if notifications expose message text. (signal.org )
- Push‑notification systems themselves became a policy flashpoint in late 2023, when Sen. Ron Wyden warned that governments can and do compel Apple and Google for push‑notification records. Those requests typically involve metadata, but the broader lesson is clear: notification pipelines and device caches can reveal more than users expect. (wyden.senate.gov )
What you can do now (iPhone)
If you use Signal (or any sensitive app) on iOS and want to minimize recoverable traces:
- Restrict previews system‑wide
- Go to Settings > Notifications > Show Previews and choose “When Unlocked” or “Never.” This prevents full message text from appearing (and being stored) when the phone is locked. (support.apple.com )
- Tighten Signal’s in‑app notifications
- In Signal, set Notification Content to “No Name or Content” (or at least “No Content”) so iOS doesn’t receive message text to display in notifications. Recent guidance highlights these options as effective mitigations. (techradar.com )
- Consider disabling lock‑screen notifications for Signal
- In iOS Settings > Notifications > Signal, turn off “Lock Screen” alerts, and use banners or badges only when unlocked. This reduces the chance of preview text persisting in lock‑screen caches. (support.apple.com )
- Keep devices updated and locked
- Strong device passcodes and up‑to‑date iOS versions raise the bar for forensic access and exploitation windows. While not foolproof, they meaningfully harden the device against extraction attempts. (cellebrite.com )
The bigger picture for investigations and policy
For investigators, the case illustrates a well‑established dynamic: device access often trumps network interception for end‑to‑end‑encrypted services. File‑system extractions can surface notification artifacts, thumbnails, caches, and other “side‑channel” traces that become admissible evidence. (enterprise.cellebrite.com )
For privacy advocates and everyday users, it’s a reminder that:
- Secure apps can’t control what the operating system stores about notifications you choose to display.
- “Disappearing messages” don’t retroactively scrub OS‑level notification caches.
- Providers like Signal publish transparency about the minimal data they hold—useful context when headlines imply a server‑side compromise. (signal.org )
Key takeaways
- The FBI did not break Signal’s encryption; it recovered incoming message text saved by iOS’s notification system on a seized iPhone. (404media.co )
- Only messages that appeared as notification previews on that device were retrievable; outgoing messages were not. (heise.de )
- Limiting or disabling notification previews—both in iOS and within Signal—reduces or eliminates this artifact. (support.apple.com )
- Server‑side, Signal can provide only basic account timestamps when compelled; it does not possess your message content. (signal.org )
As more jurisdictions and cases spotlight notification data, expect renewed scrutiny of how mobile OSes cache alerts—and more user education on locking down previews before sensitive conversations begin. (wired.com )
Related Posts
Google class action lawsuits: Where the big cases stand now and who could get paid
As of April 9, 2026: The latest on Google class actions—Play Store $700M nearing court approval, Android data $135M, Assistant $68M, and a $425.7M verdict.

Building a Production-Ready AI Image Recognition API for Mobile Apps
Design and ship a production-grade AI image recognition API for mobile apps: architecture, models, privacy, performance, and code snippets for iOS/Android.
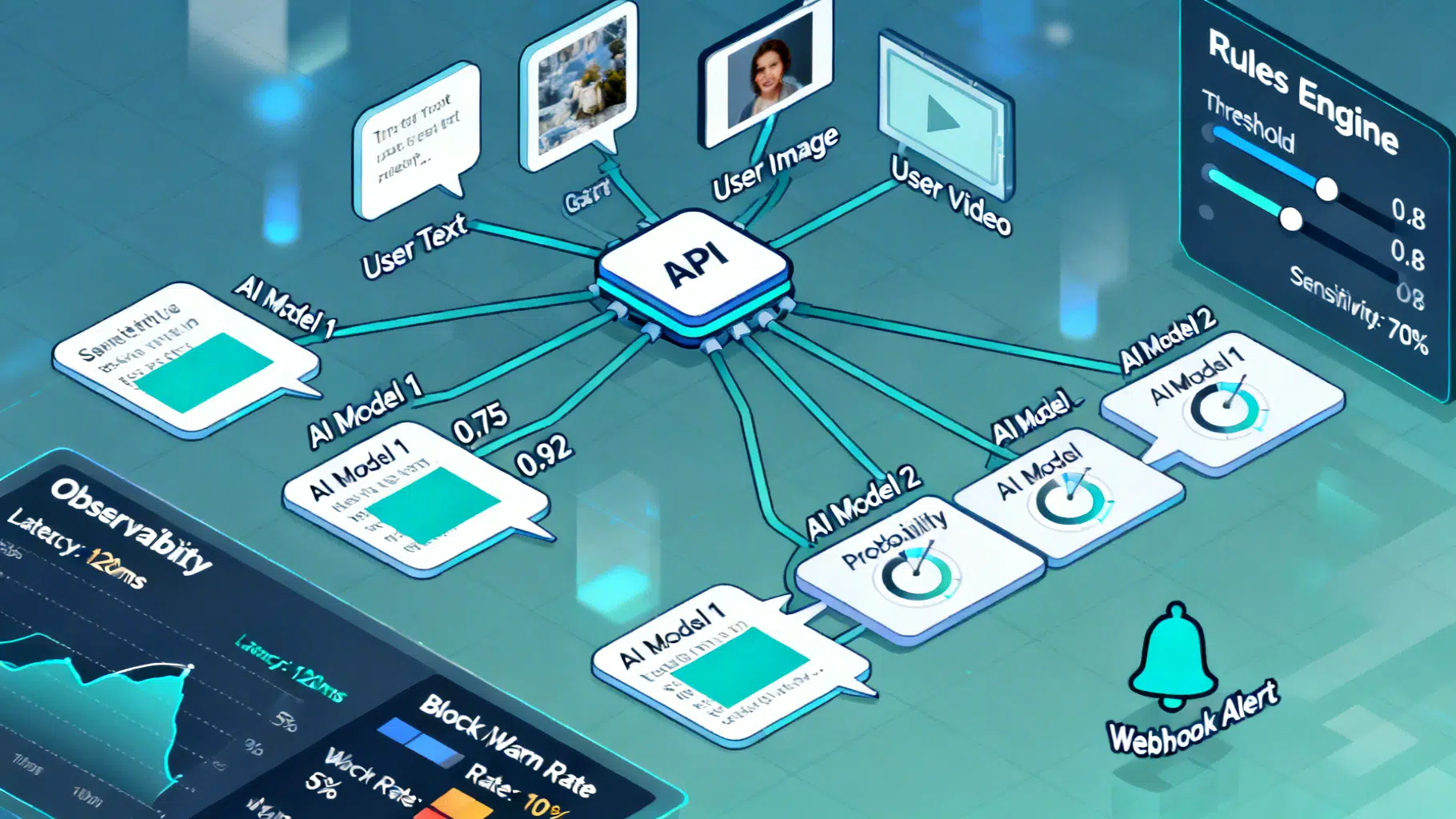
Implementing an AI Content Moderation API: Architecture, Policy, and Code
Design and implement a reliable AI content moderation API: taxonomy, architecture, code, policy config, thresholds, privacy, and evaluation best practices.
