API Backward Compatibility Strategies: Designing Change Without Breaking Clients
Practical strategies to keep APIs backward compatible—versioning, additive changes, deprecation, rollout, and testing for REST, GraphQL, and gRPC.
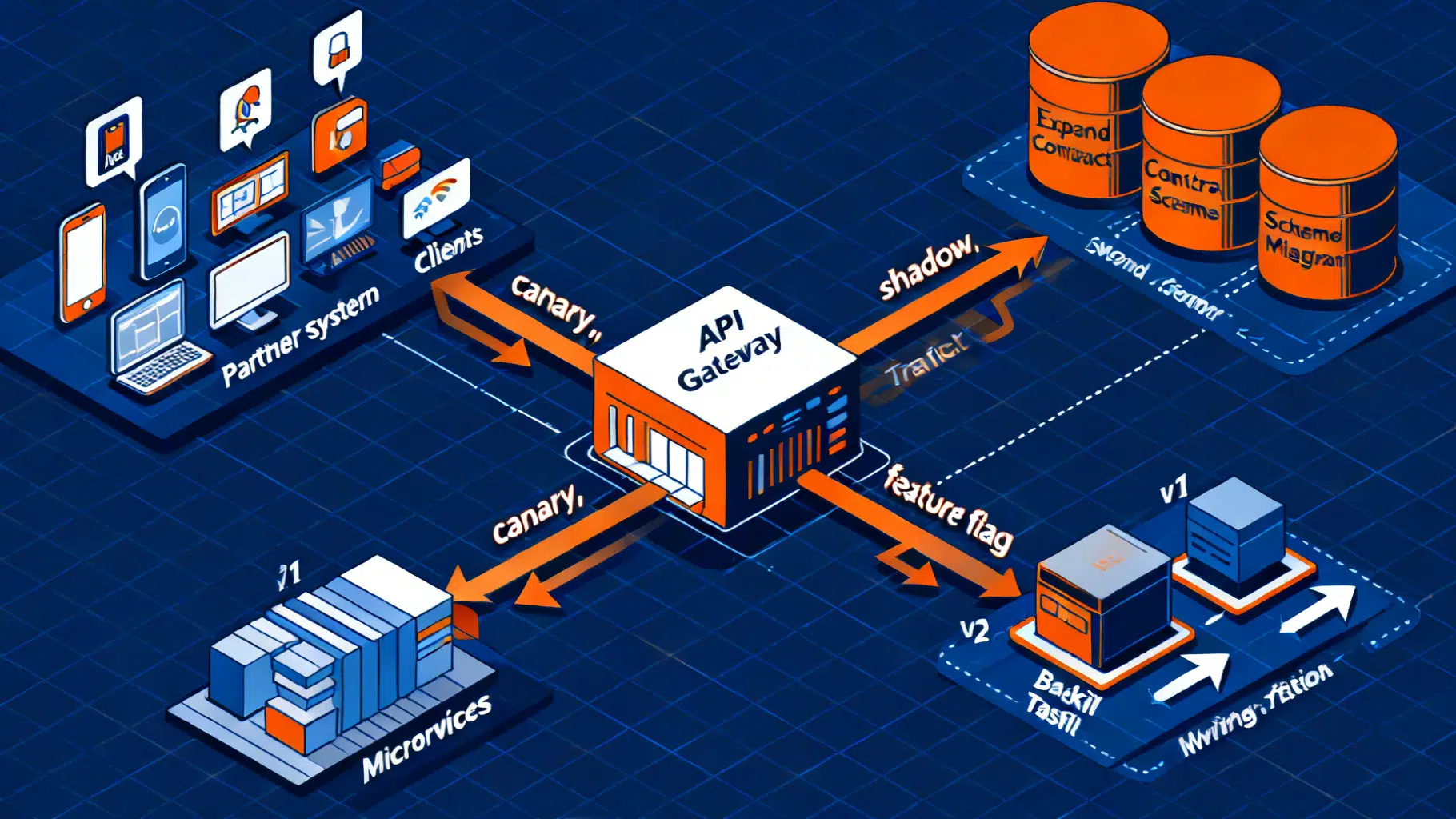
Image used for representation purposes only.
Why backward compatibility matters
APIs are long-lived contracts. Once a client ships—mobile app, IoT device, partner integration—you inherit obligations to keep their calls working. Backward compatibility means new server versions continue to accept requests created for older versions and return payloads those clients can parse without crashing or silently corrupting data.
Breakage is expensive. It triggers emergency rollbacks, damages trust, and can take months to unwind if clients are hard to update. Designing for backward compatibility from day one is cheaper than a later migration “war room.”
This article distills practical strategies for REST, GraphQL, and gRPC that let you evolve quickly while keeping existing consumers unbroken.
Define your compatibility contract
Before you change anything, write down what “compatibility” means for your platform.
- Resource model and field semantics are stable. If you change meaning, that’s a breaking change—even if the shape doesn’t change.
- Parsers must be tolerant of unexpected data. Clients should ignore unknown fields rather than failing. Servers should ignore unknown query parameters unless they alter behavior.
- Ordering is not guaranteed unless promised. Sorting or pagination without explicit contracts will eventually surprise someone.
- Error contracts are part of the API. Codes, types, and retryability are as important as success payloads.
Tip: adopt the robustness principle for clients (be liberal in what you accept) and strictness for servers (be conservative in what you emit and promise).
What changes are safe (usually)
Additive changes are the backbone of backward compatibility:
- Adding optional fields to responses
- Adding new endpoints or operations
- Adding query parameters that default to existing behavior
- Extending enums with new values if clients treat unknown values generically
- Adding HTTP headers that clients can ignore
Be careful with:
- Changing defaults or business rules (often breaking)
- Tightening validation (can start failing old requests)
- Changing data types (integer → string, number precision, timestamp format)
- Making a nullable field non-null (breaking in GraphQL and gRPC)
- Reusing deleted protobuf field numbers (always breaking)
Versioning strategies (REST)
You need a plan before the first breaking change. Pick one primary signal and stick to it across all services.
-
URI path versioning: simple, explicit, cache-friendly
- Pros: visible; easy for routing and observability
- Cons: proliferates endpoints; can fragment docs
- Example:
/v1/orders/{id}
-
Header-based versioning: cleaner URLs; lets resources evolve independently
- Example using a custom header:
curl -H 'X-API-Version: 2024-11-01' https://api.example.com/orders/123
- Media type (content negotiation): granular per-representation versions
- Example vendor media type:
curl -H 'Accept: application/vnd.example.orders+json;version=1' \
https://api.example.com/orders/123
- Date-based versions: align with release trains for public APIs
- Example:
X-API-Version: 2026-03-27
- Example:
Guidelines:
- Avoid mixing multiple primary mechanisms; it complicates routing and analytics.
- Tie your observability to the version key (dimensions in logs and metrics).
- Document which changes require a new version versus which remain additive.
Versioning beyond REST
-
GraphQL: prefer a single evolving schema. Use the
@deprecateddirective on fields and enum values. Add fields; avoid changing nullability or types. If you must break, stand up a new schema or graph, notv2inside the same endpoint. -
gRPC/Protobuf: proto3 is inherently designed for compatibility when you follow the rules:
- Never reuse or renumber field tags.
- You may add new fields with new tags (prefer optional or repeated).
- Removing a field is breaking; prefer deprecating and reserving its number.
- Unknown fields are ignored by older clients—use that.
Example protobuf showing safe evolution:
// v1
message Order {
int32 id = 1;
string status = 2; // 'pending' | 'shipped'
}
// v1.1 (additive)
message Order {
int32 id = 1;
string status = 2;
string tracking_url = 3; // optional
}
// v2 (breaking): if you remove status, reserve the tag
message Order {
int32 id = 1;
reserved 2; // do not reuse
string tracking_url = 3;
}
GraphQL deprecation example:
# v1
type Order {
id: ID!
status: String! # 'pending' | 'shipped'
}
# v1.1 (additive)
type Order {
id: ID!
status: String! @deprecated(reason: "Use fulfillmentState")
fulfillmentState: OrderFulfillmentState!
}
enum OrderFulfillmentState {
PENDING
SHIPPED
DELIVERED # added later; old clients must handle unknowns gracefully
}
Error compatibility
Define a stable error envelope from the start. Keep codes stable and treat new codes as additive.
HTTP/1.1 409 Conflict
Content-Type: application/json
{
"error": {
"code": "order_state_conflict",
"message": "Order cannot transition from SHIPPED to PENDING.",
"retryable": false,
"details": {"from": "SHIPPED", "to": "PENDING"}
}
}
Rules:
- Never recycle an error code with a new meaning.
- Expose retryability and guidance so clients can automate decisions.
- When adding new error fields, keep legacy fields present until fully retired.
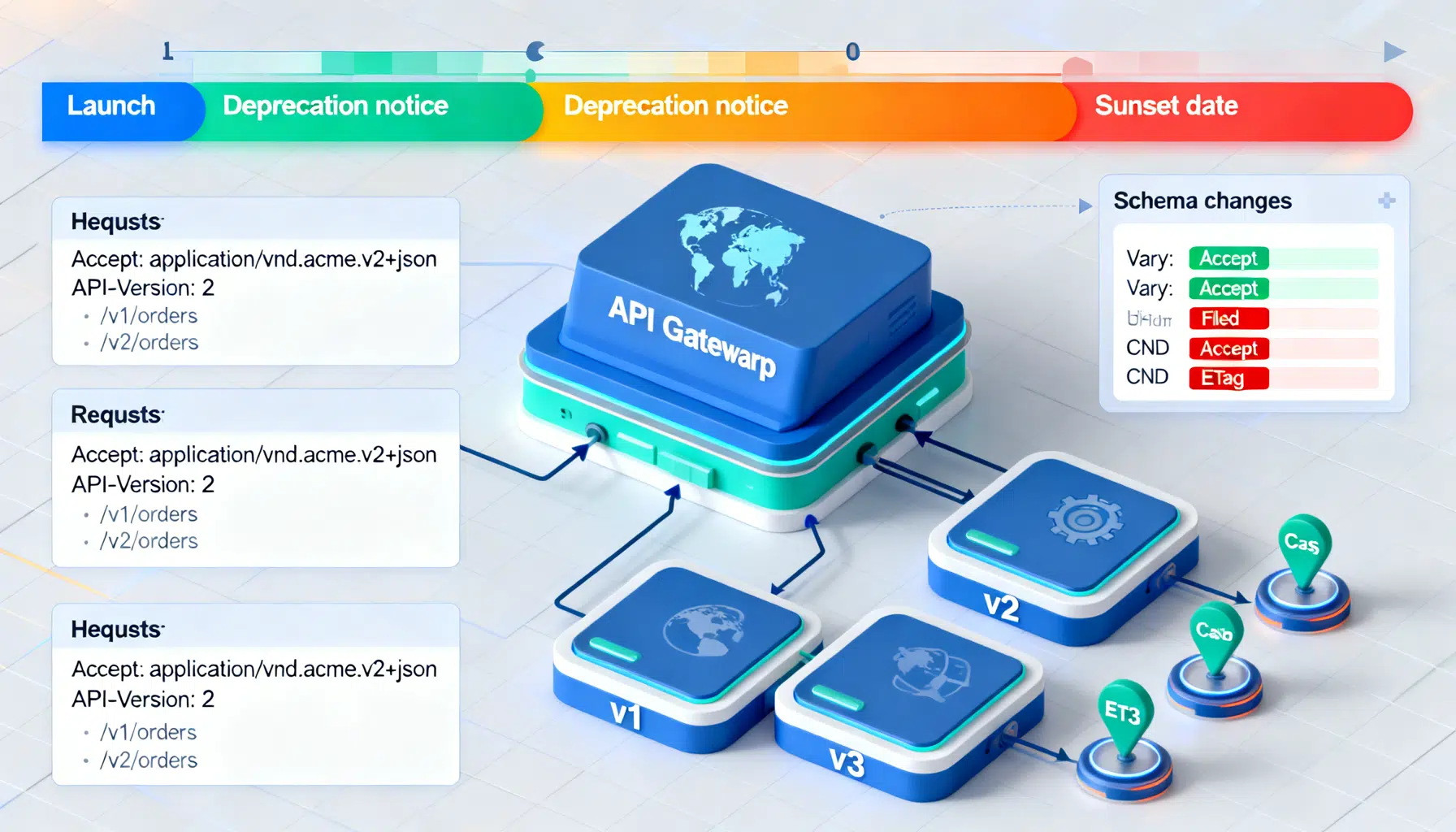
Deprecation and sunset policy
Create a written policy and publish it. It should include minimum support windows, notification channels, and a predictable timeline.
- Announce deprecations in release notes, email to registered developers, and a machine-readable changelog.
- Use standard headers to communicate:
Deprecation: version="2024-10-01"
Sunset: Fri, 01 May 2027 00:00:00 GMT
Link: </docs/migrate/orders-v1-to-v2>; rel="deprecation"; type="text/html"
- For GraphQL, set a clear end-of-life date in
@deprecated(reason: "... EOL 2027-05-01")and emit warnings in server logs for usage.
Suggested timeline template:
- T0: Public announcement and docs; begin emitting Deprecation headers
- T0 + 30 days: Reach out to top consumers with migration guidance
- T0 + 90 days: Add response warnings; start canary throttling for noncompliant test tenants
- T0 + 180 days: Restrict creation of new resources via deprecated paths
- T0 + 365 days: Sunset—disable in production with runbooks and rollback plan
Database and schema migrations: expand/contract
Most breaking changes originate in the data layer, not the transport. Use the expand/contract pattern to keep both old and new codepaths working during rollout.
Typical flow:
- Expand: add new nullable columns, tables, or indexes; keep old ones.
- Dual-write: application writes both old and new shapes.
- Backfill: migrate historical data (idempotent batches with checkpoints).
- Read-tolerant: readers can handle both schemas; prefer reading new when present.
- Flip: switch writers to new fields; monitor.
- Contract: after a safe window, remove old fields and dual-write logic.
Example (SQL + app pseudo-code):
-- Expand
ALTER TABLE orders ADD COLUMN fulfillment_state TEXT NULL;
CREATE INDEX CONCURRENTLY idx_orders_fstate ON orders(fulfillment_state);
# Backfill (idempotent): batch by primary key window
./backfill --table orders --set-fulfillment-state-from-status --from-id 0 --to-id 10_000_000
# Dual-write (simplified)
if status == 'shipped':
fulfillment_state = 'SHIPPED'
write(status=status, fulfillment_state=fulfillment_state)
Rollout patterns
- Canary releases: route a small percentage of traffic to the new version. Increase gradually while watching error budgets.
- Shadow traffic: mirror requests to the new service, discard responses, compare metrics out-of-band.
- Feature flags: gate new behavior server-side by tenant, app version, or header.
- Compatibility shims at the edge: translate v1 requests to v2 internally to buy migration time.
Example edge routing by version header (NGINX-like pseudoconfig):
map $http_x_api_version $upstream {
default legacy_v1;
~^2026- v2_cluster; # date-based versions in 2026 route to v2
}
server {
location /orders {
proxy_pass http://$upstream;
}
}
Testing for backward compatibility
Automated checks catch regressions before users do.
- Contract tests: validate provider responses match consumer expectations. Tools like Pact (HTTP) or Buf (gRPC) help.
- Schema diff gates:
- OpenAPI: block breaking diffs in CI.
- GraphQL: fail CI on non-null or type changes without proper deprecation windows.
- Protobuf: enforce reserved tags and BC-safe field changes.
- Golden snapshots: record canonical responses and compare with tolerances (e.g., ignoring added fields).
- Property-based tests: ensure clients ignore unknown fields and survive enum extensions.
Examples:
# OpenAPI diff gate
openapi-diff --fail-on-incompatible old.yaml new.yaml
# Buf for protobuf breaking-change detection
buf breaking --against .git#branch=main
Observability and SLOs by version
- Tag metrics and logs with API version, client id, and app version.
- Monitor:
- Error rates and latency per version
- Schema violations and deserialization errors
- Usage of deprecated fields/endpoints
- Distribution of client versions (to forecast sunsetting)
- Define SLOs that include compatibility aspects (e.g., <0.1% deserialization failures per day per version).
Documentation and communication
- Publish a living changelog that’s both human- and machine-readable (OpenAPI diffs, GraphQL SDL history, protobuf descriptors).
- Provide migration guides with side-by-side examples.
- Offer test sandboxes and feature-flagged previews weeks before GA.
- Keep example clients and SDKs updated first; many consumers copy from them.
OpenAPI snippet with explicit versioned media type:
{
"openapi": "3.1.0",
"info": {"title": "Orders API", "version": "1.4.0"},
"paths": {
"/orders/{id}": {
"get": {
"parameters": [{"in": "path", "name": "id", "required": true, "schema": {"type": "string"}}],
"responses": {
"200": {
"content": {
"application/vnd.example.order+json;version=1": {
"schema": {"$ref": "#/components/schemas/OrderV1"}
},
"application/vnd.example.order+json;version=2": {
"schema": {"$ref": "#/components/schemas/OrderV2"}
}
}
}
}
}
}
}
}
Common anti-patterns to avoid
- Silent breaking changes with no version bump or deprecation window
- Changing field meaning in-place (e.g., status now holds reasons)
- Tightening validation without a transition period and telemetry
- Renaming or removing protobuf fields without reserving old tags
- Overusing major versions as a crutch for every change
- “Big bang” migrations without canary/shadow phases
A practical checklist
Before coding:
- Define the goal and classify the change (additive vs breaking)
- Choose the versioning signal and update observability plans
- Draft docs and migration notes
During implementation:
- Use expand/contract in data stores
- Add compatibility shims and feature flags
- Write contract tests and CI schema diff gates
Pre-release:
- Run shadow traffic against the new version
- Canary to internal clients first; monitor per-version SLOs
- Announce deprecation timelines if applicable
Post-release:
- Track adoption and deprecated usage weekly
- Provide targeted outreach to lagging consumers
- After the window, execute the sunset with rollback steps ready
Conclusion
Backward compatibility is a product capability, not a constraint. With a clear contract, additive-first mindset, disciplined versioning, and strong testing and rollout practices, you can keep shipping changes at high velocity without breaking clients. Decide on your signals, automate your gates, communicate early, and observe everything. The payoff is compounding delivery speed and partner trust.
Related Posts
The API Versioning Playbook: Best Practices, Patterns, and Pitfalls
A practical playbook for API versioning: strategies, SemVer, backward compatibility, deprecation, testing, and rollout patterns for stable, evolving APIs.
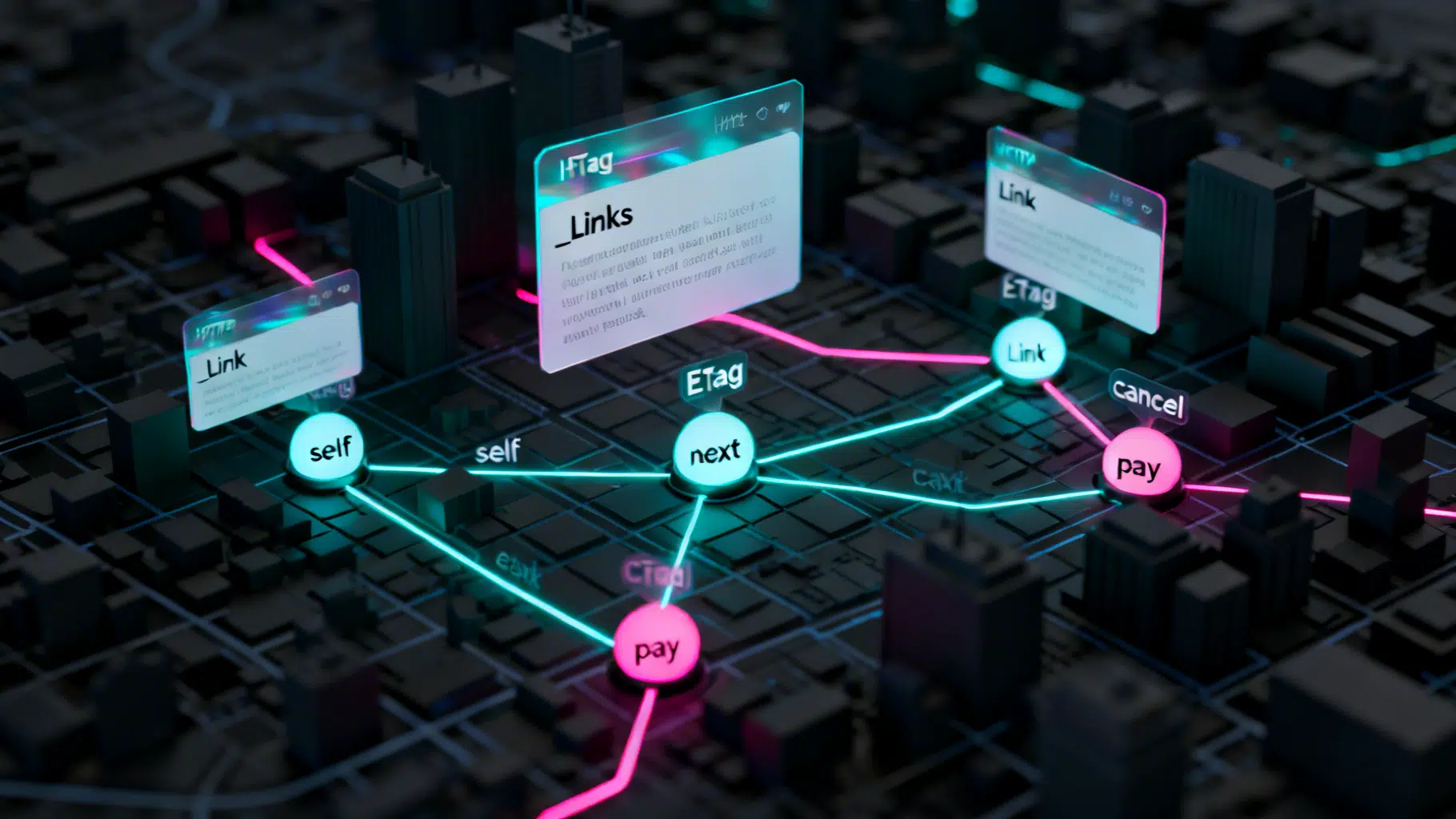
Implementing HATEOAS in REST APIs: A Practical Guide
A practical guide to implementing HATEOAS in REST APIs with formats, examples, tooling, testing, and rollout strategies.

REST API Error Handling Best Practices: A Practical, Modern Guide
A practical guide to REST API error handling: status codes, structured responses (RFC 7807), retries, rate limits, idempotency, security, and observability.
